|
Getting your Trinity Audio player ready...
|
AI innovation and adoption – both sanctioned and unsanctioned – has reached a fever pitch. Organizations are racing to invest in AI, joining a pan-industry arms race to incorporate generative and agentic AI into products and operations, often bypassing traditional security gates to maintain a competitive edge or automate time-consuming tasks.
But this rapid adoption has introduced a paralyzing fear for security teams: that a high-profile AI breach will bring the business to a grinding halt before they can implement the necessary guardrails and controls. Regulatory bodies and independent third-parties are working to keep pace and establish best practices for securing AI workloads, but business leaders and security teams are now facing a complex dilemma: You need to innovate at speed, but you cannot afford to leave your organization exposed.
Fighting Fire with Proactivity: Getting Ahead of the AI-Enabled Adversary
Making matters worse for security teams, as if they needed more of a challenge, is the fact that while AI amplifies IT complexity and extends the attack surface, it’s also serving as a force multiplier and accelerator for threat actors looking to weaponize AI innovation. Whether it’s increasing the speed or volume of attacks or using AI to find the achilles heel of an organization’s security controls, AI is helping attackers be more efficient and effective just as it is helping security teams.
One solution to this problem is to fight fire with fire, using AI within security tools to detect more, faster and bubble up the insights that really matter to defenders in the fog of war. That’s of course helpful, but it’s not enough, and if history has taught us anything it’s that trying to out-run or out-muscle adversaries is a losing endeavor. The only way security teams can truly overcome the rising threat of AI-powered attackers is to take proactive action, sifting through the noise to highlight and fix the issues that actually let attackers compromise the business.
Where Exactly Scanners Break Down Across the CTEM Lifecycle
The Complexity of the Modern Attack Surface
The reality of the modern attack surface is that employees across the entire business, – whether they sit in Finance, marketing or software development – are using AI to work smarter, ship faster and meet ever-rising business expectations. This adoption often happens before the security team can put in the proper security controls or establish organizational best practices and policies.The challenge starts with the fundamentals, with teams often lacking basic visibility into exactly where AI models, agents, and data sets are being deployed across both on-prem and cloud environments, or what public AI applications employees are sharing sensitive company data with.Traditional security perimeters were built to defend static, well-defined workloads where “normal” behavior was easy to baseline. AI-driven environments, particularly those utilizing the Model Context Protocol (MCP), introduce a new layer of complexity that often bypasses standard monitoring.
These modern AI workloads differ from traditional environments in three critical ways:
- Decentralized Credentials: In traditional apps, secrets are typically managed by centralized vaults; however, AI developers often hardcode API keys directly into Markdown instruction files to simplify agent workflows, creating “gold mines” for attackers.
- The “Local” Attack Surface: Traditional security focuses on external network traffic. In contrast, AI vulnerabilities like CVE-2025-6514 leverage local workstation processes to execute commands through a browser, effectively turning a developer’s own machine against them.
- Dynamic Command Execution: Standard workloads rarely change their execution patterns. AI agents, however, are designed to be flexible, often requiring shell interpreters like bash or powershell to function. This makes it incredibly difficult for security teams to distinguish between a legitimate AI task and a malicious Remote Code Execution (RCE) attempt.
Extending Continuous Exposure Management to the AI Attack Surface
At XM Cyber, we are continuously evolving our platform to secure your AI-driven innovation and there are two recent releases that are particularly exciting: AI Discovery Dashboard and AI Attack Paths.
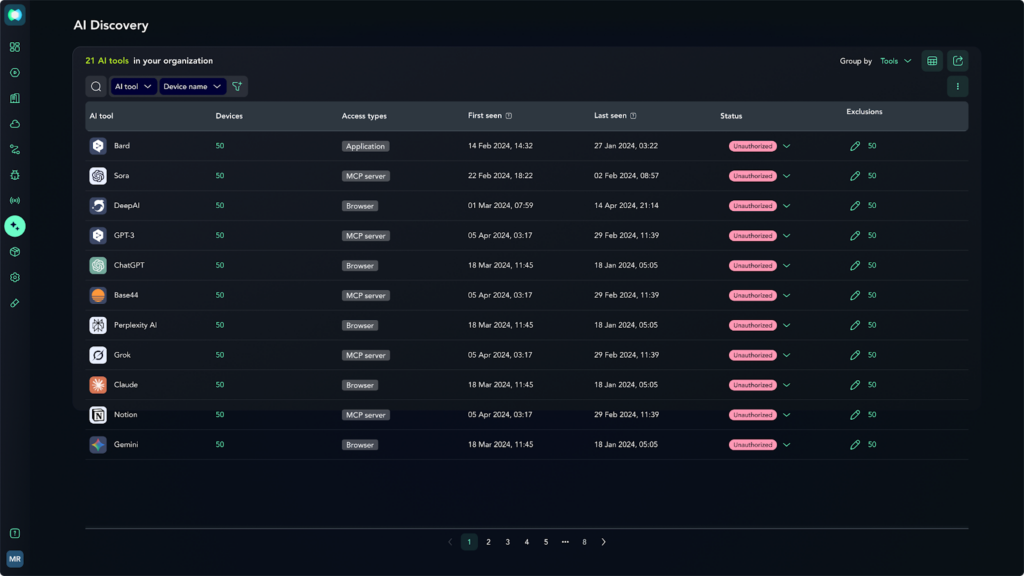
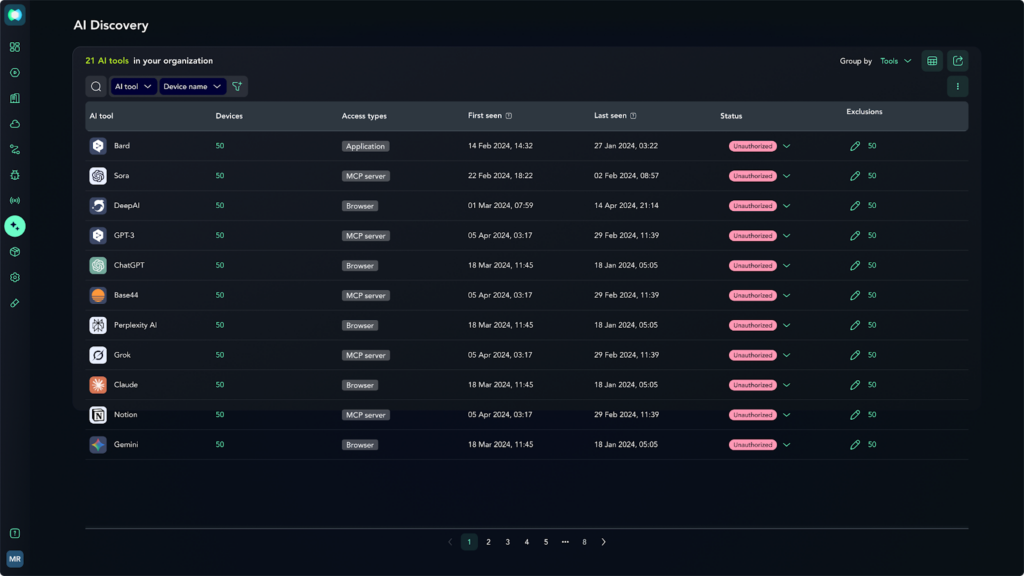
- Discover Shadow AI
Taking aim at shadow AI usage and gaps in attack surface coverage, we’ve released a new centralized dashboard that brings together a real-time view of employee AI usage across popular AI tools including browsers, MCP servers, and installed apps as well as public services such as OpenAI, Claude, Cursor and more. By continuously discovering AI applications in use across the organization, we help you eliminate shadow AI and assess potential exposure of sensitive company data in real-time.
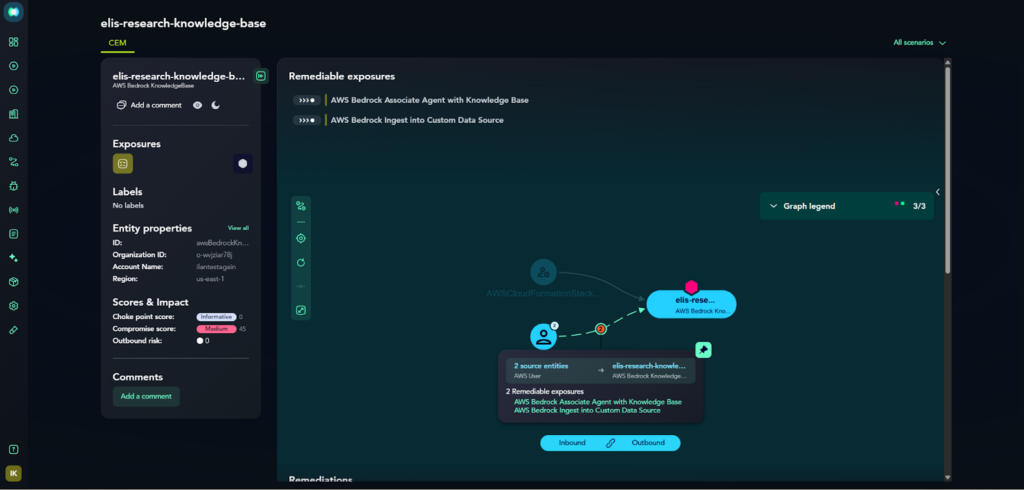
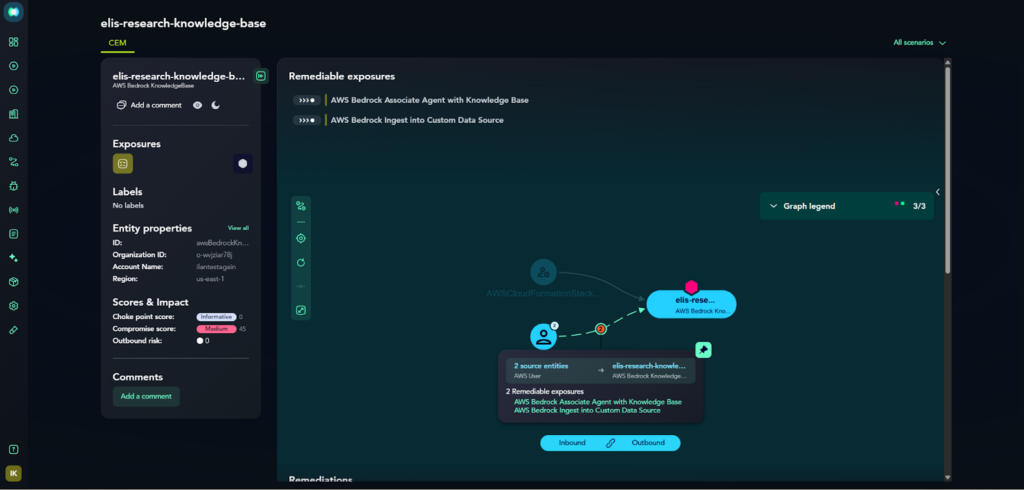
- See & Fix AI Exposures on Attack Paths
We’ve also extended Attack Graph AnalysisTM to the AI attack surface, uncovering exactly how attackers would utilize exposures in AI development and training resources like AWS Bedrock and Azure OpenAI to traverse your on-prem and cloud environments to compromise your business and sensitive data. Our platform keeps AI security out of technology and operating silos, proactively identifying and dynamically mapping these validated paths across the entire attack surface for efficient remediation. This approach ensures misconfigured AI resources – no matter where they are across your environment – don’t indirectly put your critical assets at risk.
Adopt AI Without Compromise
You shouldn’t have to choose between AI-driven innovation and organizational security. XM Cyber can help your team adopt AI securely and proactively eliminate exposures before AI-powered attackers can exploit them. Be sure to reach out today for a demo to see for yourself!
AI innovation and adoption – both sanctioned and unsanctioned – has reached a fever pitch. Organizations are racing to invest in AI, joining a pan-industry arms race to incorporate generative and agentic AI into products and operations, often bypassing traditional security gates to maintain a competitive edge or automate time-consuming tasks.
But this rapid adoption has introduced a paralyzing fear for security teams: that a high-profile AI breach will bring the business to a grinding halt before they can implement the necessary guardrails and controls. Regulatory bodies and independent third-parties are working to keep pace and establish best practices for securing AI workloads, but business leaders and security teams are now facing a complex dilemma: You need to innovate at speed, but you cannot afford to leave your organization exposed.
Fighting Fire with Proactivity: Getting Ahead of the AI-Enabled Adversary
Making matters worse for security teams, as if they needed more of a challenge, is the fact that while AI amplifies IT complexity and extends the attack surface, it’s also serving as a force multiplier and accelerator for threat actors looking to weaponize AI innovation. Whether it’s increasing the speed or volume of attacks or using AI to find the achilles heel of an organization’s security controls, AI is helping attackers be more efficient and effective just as it is helping security teams.
One solution to this problem is to fight fire with fire, using AI within security tools to detect more, faster and bubble up the insights that really matter to defenders in the fog of war. That’s of course helpful, but it’s not enough, and if history has taught us anything it’s that trying to out-run or out-muscle adversaries is a losing endeavor. The only way security teams can truly overcome the rising threat of AI-powered attackers is to take proactive action, sifting through the noise to highlight and fix the issues that actually let attackers compromise the business.
Where Exactly Scanners Break Down Across the CTEM Lifecycle
The Complexity of the Modern Attack Surface
The reality of the modern attack surface is that employees across the entire business, – whether they sit in Finance, marketing or software development – are using AI to work smarter, ship faster and meet ever-rising business expectations. This adoption often happens before the security team can put in the proper security controls or establish organizational best practices and policies.The challenge starts with the fundamentals, with teams often lacking basic visibility into exactly where AI models, agents, and data sets are being deployed across both on-prem and cloud environments, or what public AI applications employees are sharing sensitive company data with.Traditional security perimeters were built to defend static, well-defined workloads where “normal” behavior was easy to baseline. AI-driven environments, particularly those utilizing the Model Context Protocol (MCP), introduce a new layer of complexity that often bypasses standard monitoring.
These modern AI workloads differ from traditional environments in three critical ways:
- Decentralized Credentials: In traditional apps, secrets are typically managed by centralized vaults; however, AI developers often hardcode API keys directly into Markdown instruction files to simplify agent workflows, creating “gold mines” for attackers.
- The “Local” Attack Surface: Traditional security focuses on external network traffic. In contrast, AI vulnerabilities like CVE-2025-6514 leverage local workstation processes to execute commands through a browser, effectively turning a developer’s own machine against them.
- Dynamic Command Execution: Standard workloads rarely change their execution patterns. AI agents, however, are designed to be flexible, often requiring shell interpreters like bash or powershell to function. This makes it incredibly difficult for security teams to distinguish between a legitimate AI task and a malicious Remote Code Execution (RCE) attempt.
Extending Continuous Exposure Management to the AI Attack Surface
At XM Cyber, we are continuously evolving our platform to secure your AI-driven innovation and there are two recent releases that are particularly exciting: AI Discovery Dashboard and AI Attack Paths.
- Discover Shadow AI
Taking aim at shadow AI usage and gaps in attack surface coverage, we’ve released a new centralized dashboard that brings together a real-time view of employee AI usage across popular AI tools including browsers, MCP servers, and installed apps as well as public services such as OpenAI, Claude, Cursor and more. By continuously discovering AI applications in use across the organization, we help you eliminate shadow AI and assess potential exposure of sensitive company data in real-time.
- See & Fix AI Exposures on Attack Paths
We’ve also extended Attack Graph AnalysisTM to the AI attack surface, uncovering exactly how attackers would utilize exposures in AI development and training resources like AWS Bedrock and Azure OpenAI to traverse your on-prem and cloud environments to compromise your business and sensitive data. Our platform keeps AI security out of technology and operating silos, proactively identifying and dynamically mapping these validated paths across the entire attack surface for efficient remediation. This approach ensures misconfigured AI resources – no matter where they are across your environment – don’t indirectly put your critical assets at risk.
Adopt AI Without Compromise
You shouldn’t have to choose between AI-driven innovation and organizational security. XM Cyber can help your team adopt AI securely and proactively eliminate exposures before AI-powered attackers can exploit them. Be sure to reach out today for a demo to see for yourself!






