Julius Caesar famously said, “Experience is the best teacher.” Yet no organization wants to learn by experience when it comes to cloud security breaches. Instead, it’s better to learn from the examples of other organizations that have endured their own cloud data breach incidents.
Over the past few years, there has been no shortage of high-profile examples to study.
With that in mind, let’s take a closer look at five of the highest-profile cloud breaches in history. Then, we’ll review some steps that can help prevent such scenarios from unfolding, including the implementation of an advanced breach and attack simulation platform that offers unique protection for hybrid environments.
A List to Avoid: Some of the Worst Cloud Security Breaches of All Time
- In the summer of 2019, Capital One suffered a breach that exposed the financial data of more than 100 million consumers. A Seattle woman was later charged with stealing this data from a misconfigured Amazon Web Services (AWS) server.
- The hotel operator Marriott had the misfortune of suffering one of the largest and longest data breaches in history. Hackers initially began stealing data from another hotel operator, Starwood, in 2014. The intrusion had not been detected when Marriott acquired Starwood two years later. It would take another two years before the attackers were discovered. By that time, they had escaped with data associated with 500 million Starwood and Marriott customers.
- In April of 2019, 540 million Facebook-related records, collected by two third-party vendors and stored on AWS, were accidentally exposed to the public. By failing to set the servers to private, Facebook account passwords, names, likes, photos, etc., were exposed to the world. The following month, Facebook admitted to storing the passwords of millions of Instagram users in unencrypted plaintext, a significant security lapse.
- In June 2019, a debt collection firm called American Medical Collection Agency was victimized by a breach that resulted in patient data being exposed and a flurry of fraudulent credit card charges. In an ironic twist, the company subsequently sought bankruptcy protection from creditors.
- In 2016, the Mexican National Electoral Institute accidentally exposed the names, birth dates, addresses and other identifying information of 93 million Mexican voters. The incident created an outcry in Mexico, especially after it was revealed that the country’s critical voter ID data was stored on a misconfigured cloud server located in another country.
You’ve likely noticed a pattern at this point: One simple mistake (in most of these cases, an AWS configuration error) can lead to devastating consequences. Fortunately, by taking a closer look at common hybrid cloud security threats (and by practicing smart hybrid cloud hygiene), organizations can limit their chances of having to learn this hard lesson by experience.
Common Threats in Hybrid Cloud Environments: What to Look For
So how does an enterprise avoid joining next year’s list of infamous breaches? By focusing on some of the most pressing hybrid IT threats. Here’s a list of the most common reasons organizations fall short at maintaining cloud security.
- Failing to perform a detailed assessment of security risks. Comprehensive risk profiles of IT systems and infrastructure play a critical role in preventing breaches and helping to remediate them should they occur.
- Not implementing adequate encryption. All transmissions should be protected by strong cryptography, including endpoint authentication.
- Inadequate awareness of the interplay between hybrid environments. Defenders must consider how each environment affects the other in terms of security challenges.
- Not maintaining proper hybrid cloud hygiene. In an environment that’s growing ever more complex, it’s essential for all team members to remain compliant with smart security protocols.
- Failing to protect the most critical assets. Intellectual property and other “crown jewel” assets need added protection from Advanced Persistent Threats (APTs) and other risks. These assets must have the tightest security controls and encryption possible.
- Taking a reactive posture toward hybrid cloud security. Without continuous monitoring of the security landscape, it’s almost impossible to maintain an even playing field for defenders.
Now that we’ve covered some of the most critical threats, let’s take a closer look at why a breach and attack simulation for hybrid cloud environments is the best current option for mitigating these risks.
The Benefits of a Breach and Attack Solution for Hybrid Cloud Environments
As mentioned above, a reactive posture is a significant disadvantage for defenders, who must contend with the ever-growing complexity of the cloud, the specific challenges inherent to hybrid environments and the skill and malicious intent of APTs.
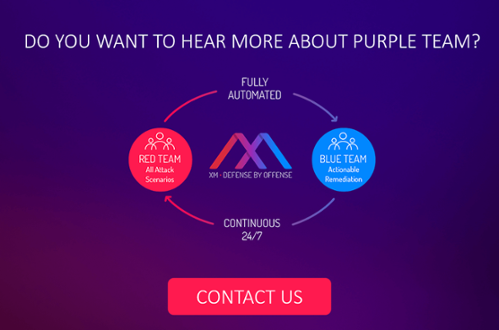
Breach and attack simulations allow defenders to take the initiative and adopt the mindset of the attacker. These platforms launch simulated attacks in a controlled environment in a manner that is akin to automated red teaming. Yet unlike red team testing, which is manual and episodic, these simulations are both automated and continuous, which means they can provide organizations with a clear picture of their overall security on a 24/7, 365 basis.
XM Cyber has introduced the world’s first breach and attack simulation platform designed for hybrid cloud environments. XM Cyber’s platform can simulate attacks on AWS, identifying vulnerabilities and helping to ensure that critical assets remain protected. As seen in the examples of breaches above, hackers often capitalize on misconfigurations and faulty security practices. The reason why is simple: Humans are prone to mistakes, and always will be.
Recognizing this fact, one thing is clear: The only way to achieve robust protection in a landscape where mistakes are inevitable is continuous testing. Without the kind of automated and continuous protection offered by the XM Cyber platform, defenders are forced into a reactive position — and have much more limited visibility into vulnerabilities in hybrid environments.
In Conclusion
Breach and attack simulations are the best tool for maintaining continuous visibility into organizational vulnerabilities — and XM Cyber has the market’s first and only breach and attack platform for hybrid environments. Defenders seeking to even the playing field should seize the initiative by deploying an advanced breach and attack solution — something that will lower the odds of learning a tough first-hand lesson about hybrid security.
By John Macintosh, Senior Field Engineer, XM Cyber
Related Topics