|
Getting your Trinity Audio player ready...
|
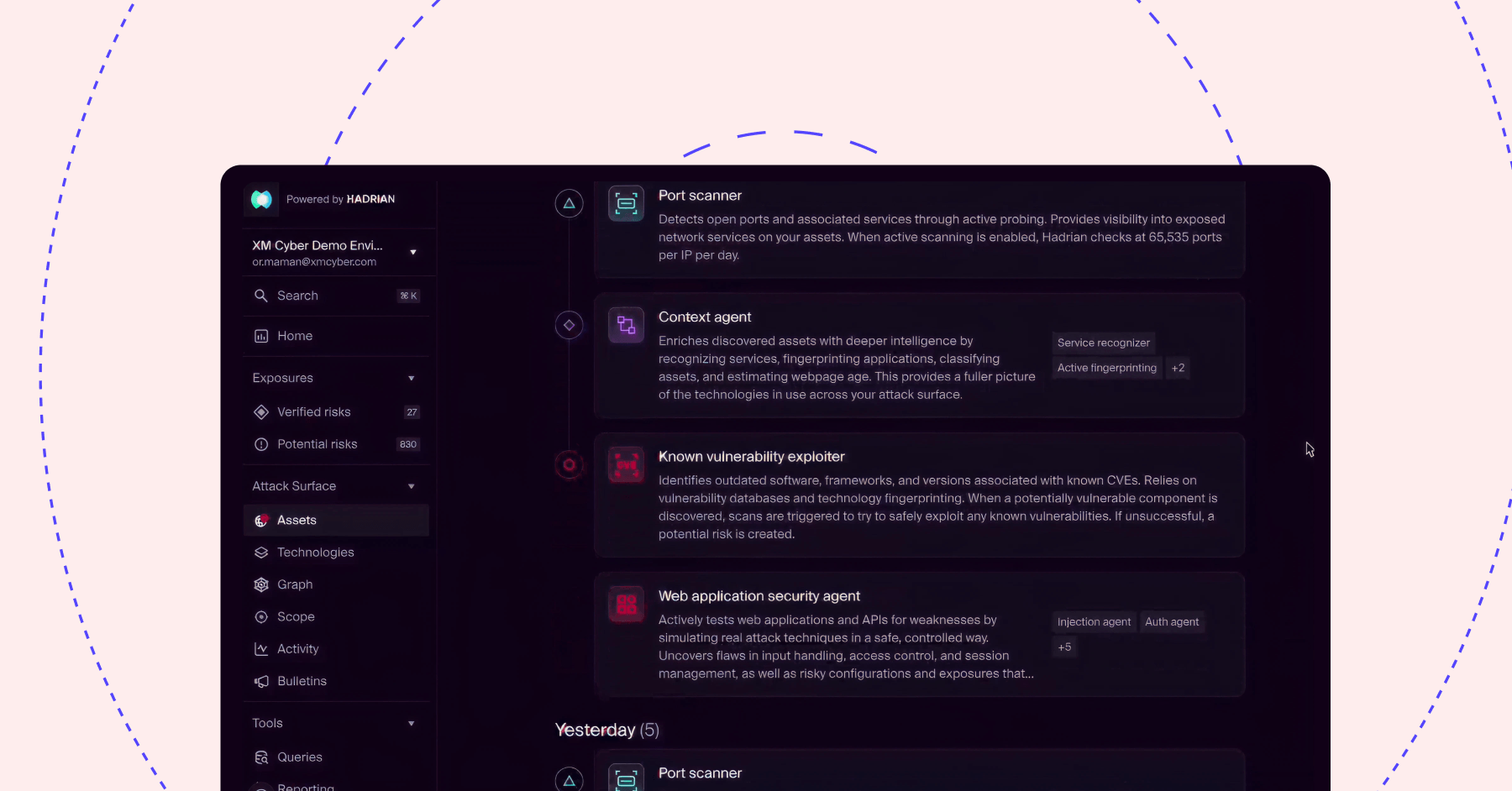
XM Cyber links the external attack surface directly to the blast radius of external exposures on critical business assets. Watch the video to see how we uniquely map external facing assets into the internal network and run a proprietary, attacker-centric two-step validation to ensure you fix what matters.