|
Getting your Trinity Audio player ready...
|
To catch a criminal, you need to think like a criminal. This is not a new concept, and it’s one that has been employed and talked about in cybersecurity for decades. It makes sense in theory. The only way to really get ahead of an adversary looking to breach your network and compromise your business is to look at that network through their eyes, understanding where they’d look for gaps and what types of exposures they’d look to weaponize on their journey.
In practice, however, this tends to be much easier said than done. Most organizations struggle to achieve the foundational attack surface visibility required because their existing toolsets have them looking at their attack surface in siloed pockets, creating blind spots and causing them to miss the forest for the trees.
Bridging the Silos: The End-to-End View
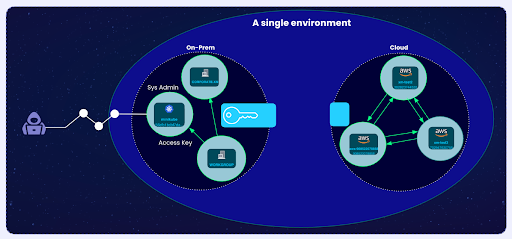
Attackers aren’t looking for a “Critical” vulnerability; they are looking for a way in. They’re looking to take one step at a time, often traversing a variety of asset types, weaponizing a mix of exposure like exposed credentials, overly-permissive roles, or misconfigured storage buckets to ultimately gain access to the sensitive data they’re looking for.
While we see “Silo A” (a misconfigured S3 bucket) and “Silo B” (a leaked API key), we often fail to see the logical bridge between them. If your visibility stops at the edge of a specific tool’s integration, you aren’t managing risk; you’re managing a list.
Driving Cross-Functional Alignment and The “Burden of Proof”
One of the often overlooked challenges that security teams face actually comes after exposures are identified and prioritized. For most organizations, the security team owns the risk and is responsible for proactively addressing issues before they’re weaponized. However, very few of these teams actually have the authority to force action – often relying on influencing a cross-functional team of stakeholders to comprehensively remediate issues when they arise.
Without validation, your team is forced to chase every high-severity alert regardless of whether it’s actually reachable or exploitable. This doesn’t just waste time; it creates cognitive fatigue, where the alerts that actually matter get buried in the noise of false positives. This is where the standard approach to exposure management often fails. Most teams rely on passive scanning to identify external exposures. While useful for discovery, running a passive scan is bound to present you with a long list of potential exposures that don’t actually put your business at risk.
Cross-functional stakeholders in IT, Cloud, and DevOps have their own roadmaps. When security asks them to pivot, or spend time going back to fix issues missed in previous sprints, the natural response is: “Why? What is the actual risk? Is this a priority?”
Overcoming the Burden of Proof With Evidence of Exposure and Impact
The best way to overcome these types of objections is evidence. If you can’t prove that an exposure is reachable and leads to a critical asset, you lack the evidence needed to overcome this burden of proof.
This is where a dual-pronged validation strategy changes the conversation:
- From the Outside: Use active scanning to move beyond “passive guessing.” By safely testing and scraping the perimeter, you prove whether a door is truly unlocked or if it can be easily picked.
- On the Inside: Use a digital twin to uncover interconnected exposures and attack paths, continuously testing exploit conditions. This allows you to safely simulate lateral movement and blast radius without the risk of disrupting production availability.
By providing evidence of exposure from the outside-in and inside-out, the security team is able to drive urgency with proof that the risk is real and a threat could be imminent.