We’ve all heard it stated ad nauseam: Cyber data breaches are continually growing and pose an urgent threat to global business. Yet is that message truly sinking in? Do corporate leaders place a priority on understanding data breaches and their impact? Or are the tools that organizations deploy simply inadequate for the task?
In 2019, a landmark event occurred in data breach history: The Yahoo! board of directors agreed to pay a $29 million settlement to company shareholders in the wake of a breach that resulted in roughly three billion user accounts being exposed. This marked the first time a company’s shareholders had ever held a company fiscally responsible for a data breach. It should have been (yet another) obvious signal to corporations that cybersecurity should be a top strategic priority.
Over the subsequent year, however, little has changed. 2019 went on to set another historic mark for the number of records exposed in data breaches. The cost of an individual data breach now averages almost $4 million and continues to rise each year. In certain fields, such as healthcare, the average cost of a breach is even higher (roughly $6.5 million). The combined global cost of all breaches is now in the trillions, annually.
Given the risks businesses face ― and the fact that corporate boards are now more likely to be held responsible ― it’s time to ramp up organizational defenses and wield the right tools for the job.
Why Cybersecurity Risks Are Rising
According to research from Cisco, nearly one-third of corporations report experiencing a cyber-attack. Let’s take a closer look at a few of the factors that are increasing risk for organizations in 2020.
- Cloud migration. Today’s corporations want the cost benefits and scalability associated with the cloud and are pushing to migrate. However, this exposes the organization to a certain level of risk that must be managed. If you’re backing up data offline, other virtual machines may access this data and possibly expose your cryptographic keys. In addition to specific risks, defenders must contend with the general problem of cloud/hybrid complexity and understand how cloud and on-prem environments impact each other in terms of security.
- Insider threats are on the rise. According to the 2019 “Insider Threat Intelligence Report,” insider threats continue to spike, and companies are now paying more than $8 million to resolve each incident. Poor IT hygiene and negligence are responsible for 64% of these attacks, while compromised user credentials are involved in 13% of insider attacks. These numbers illuminate the need for comprehensive and regular training, as even the most advanced technical solution can be undermined by simple human oversight.
- The threat of ransomware attacks may be understated. According to Verizon’s annual Data Breach Investigations Report (DBIR), 24% of all malware incidents involve ransomware. Yet healthcare organizations (which are required by law to disclose any breach that occurs due to HIPAA regulations) report a much higher figure: 70%. Could this mean that organizations (most of which are not subject to strict reporting rules) are underreporting ransomware attacks? Corporate security teams need to keep the threat of ransomware top of mind this year and beyond, given their potential for causing serious harm.
- Third-party and supply chain attacks are growing more prominent. Why? Cloud computing has increased the need to work with vendors for services and software, and attackers seek the weakest point in any chain. A large enterprise may have robust security, yet may be exposed by sub-standard security practices of a vendor.
- Cybersecurity risk management isn’t yet a core strategic priority for many entities. Too many organizations still view security as a standalone domain within IT rather than something that permeates every level of a business. To truly get organization security right, it’s important to view critical business objectives or operations through the prism of cybersecurity. It’s not acceptable to keep organizational security siloed and delegated to the CISO or CIO because the rest of the leadership has a difficult time grasping the finer points. The entire organization needs to buy in to effectively plan for risks. This extends beyond mere policy setting and into the realm of personal security practices; the DBIR reports that C-suite executives are being directly targeted by hackers in larger numbers.
Why a Data Breach Simulation Platform Is the Answer
As we’ve outlined, maintaining comprehensive security requires a strong commitment through every layer of an organization. Yet the right tools are an equally important part of the solution.
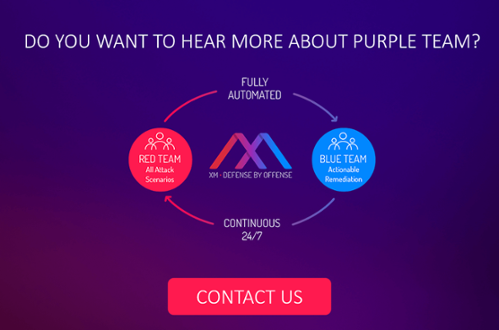
A breach and attack (BAS) platform offers the strongest defense against cyber-attacks, as it allows for continuous, automated testing. A BAS platform will launch simulated attacks in a controlled environment, a process that is much like conventional penetration testing. Yet instead of relying on manual testers, BAS platforms run simulations on a 24/7, 365 basis ― allowing organizations unparalleled insight into the minute by minute state of their security defenses.
XM Cyber has created the market’s most advanced BAS solution ― and the only such platform that can simulate attacks in hybrid environments, making it an essential tool during cloud migration. For organizations seeking to get ahead of the curve (and ahead of attackers) on cybersecurity, a platform that offers automated and continuous testing across multiple environments is the gold standard.
Shahar Solomon is Customer Operations Manager, XM Cyber
Related Topics