Building and Scaling Secure Agentic AI Applications in AWS Bedrock
The transition from passive Generative AI to Agentic AI has fundamentally rewritten the cloud security playbook. While early defenses focused…
eBooks & Whitepapers
Navigating the Exposure Management Space: A Buyer’s Guide
Behind every successful breach is a chain of interconnected failures—a stolen password, a missing patch, over-permissions, a misconfigured S3 bucket.…
eBooks & Whitepapers
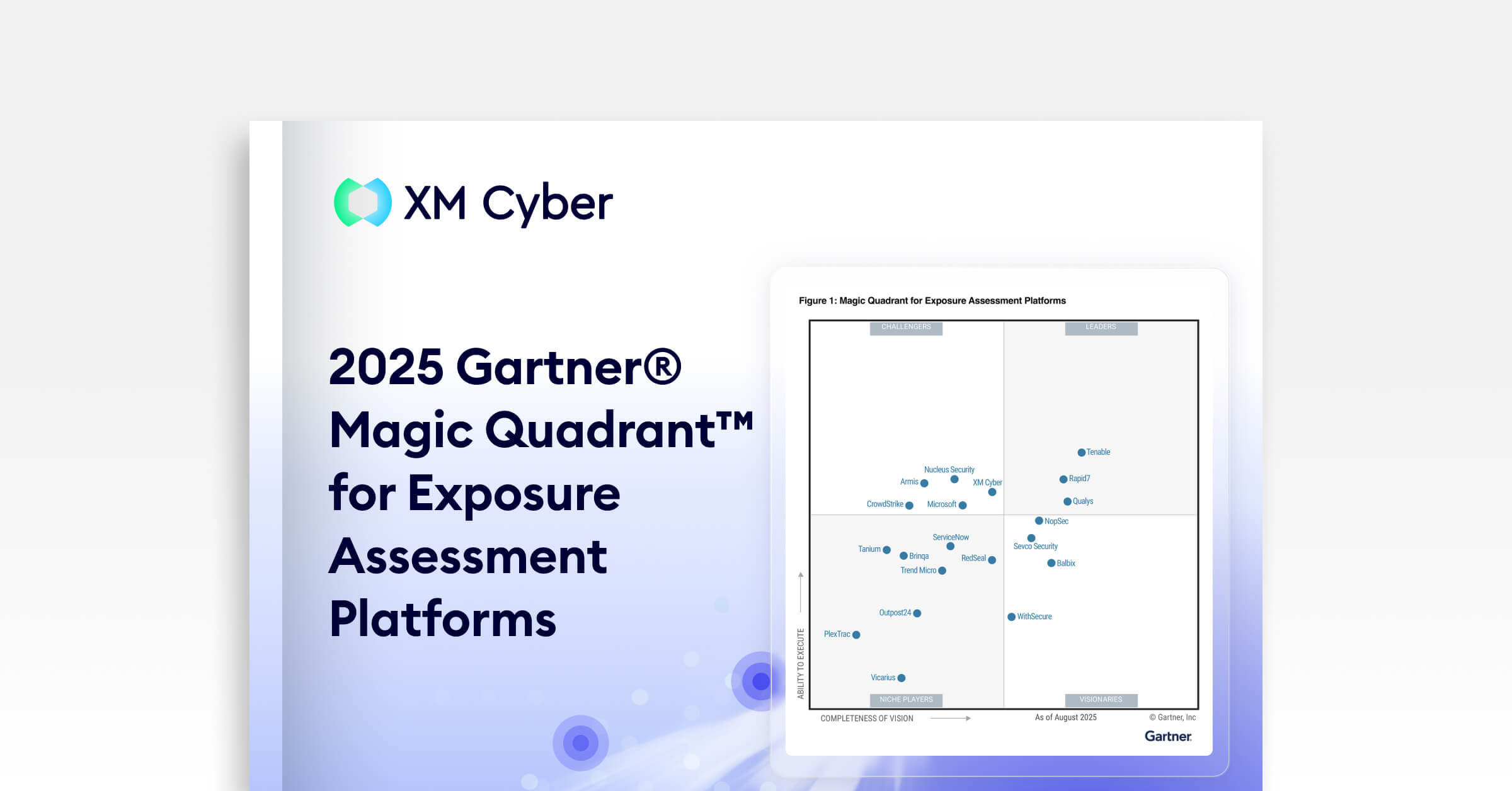
XM Cyber Named a Challenger in 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms
We’re proud to be named a Challenger in the first-ever Gartner Magic Quadrant for Exposure Assessment Platforms. We believe our…
eBooks & Whitepapers
From Reactive to Resilient: Navigating the New Era of Cyber Compliance
Compliance isn’t a back-office task anymore – it’s at the heart of how organizations manage risk, ensure resilience, and build…
eBooks & Whitepapers
Wondering How to Transform Complex Requirements into Sustainable Operations?
With each new regulation, security teams face the same challenge: turning complex requirements into practical, sustainable operations. Regardless of the…
eBooks & Whitepapers
Navigating the Paths of Risk: The State of Exposure Management in 2024
This report presents key insights drawn from hundreds of thousands of attack path assessments conducted through the XM Cyber Continuous…
eBooks & Whitepapers
Understanding the NIS 2 Directive with XM Cyber
Are you trying to understand what the new NIS 2 Directive means for your organization? The EU’s new NIS 2…
eBooks & Whitepapers
The 5 Stages of CTEM – Your Guide to Making Them a Reality
Wondering how to make CTEM a reality in your organization in 2025? The Continuous Threat Exposure Management framework has proven…
eBooks & Whitepapers
Breaking Attack Paths to Legacy and OT Systems
Securing Legacy and OT systems require a different approach. Outdated architecture, lack of software updates and patches, and systems that…
eBooks & Whitepapers
The First 90 Days as CISO – Your Roadmap to Success
They say you never get a second chance to make a first impression. And accordingly, your first 90 days in…
eBooks & Whitepapers
How Attackers (Really) Advance: Unveiling 11 Real-Life Stories
Attackers are constantly on the hunt for the quickest and easiest paths to your critical assets, using a combination of…
eBooks & Whitepapers
A CISO’s Guide to Reporting Risk to The Board
If the thought of reporting to your Board makes you more than a bit nervous, don’t worry you’re in good…
eBooks & Whitepapers
See XM Cyber In Action