|
Getting your Trinity Audio player ready...
|
What Are Active Directory Security Best Practices?
Active Directory (AD) security refers to the strategies, tools, and configurations used to protect an organization’s Active Directory environment from unauthorized access, abuse, and compromise. Because AD is a critical component in most Windows-based enterprise networks, it often becomes a primary target for attackers.
AD security best practices involve safeguarding user credentials, group memberships, domain controllers, and authentication mechanisms. They also include hardening AD configurations, enforcing least privilege, and continuously monitoring for signs of lateral movement or privilege escalation.
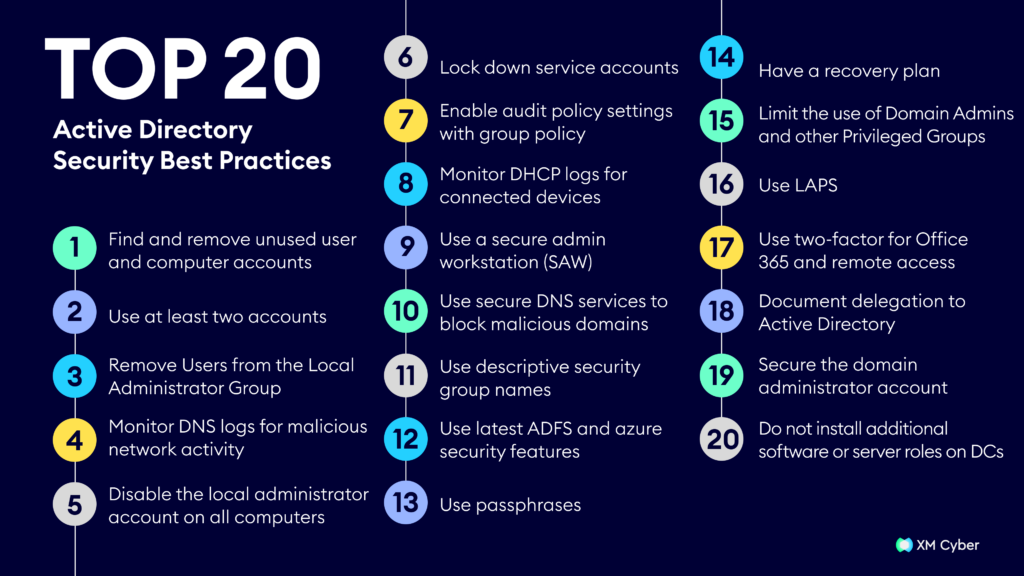
In this article we’ll cover the following active directory security best practices:
- Find and remove unused user and computer accounts
- Use at least two accounts
- Remove Users from the Local Administrator Group
- Monitor DNS logs for malicious network activity
- Disable the local administrator account on all computers
- Lock down service accounts
- Enable audit policy settings with group policy
- Monitor DHCP logs for connected devices
- Use a secure admin workstation (SAW)
- Use secure DNS services to block malicious domains
- Use descriptive security group names
- Use latest ADFS and azure security features
- Use passphrases
- Have a recovery plan
- Limit the use of Domain Admins and other Privileged Groups
- Use LAPS
- Use two-factor for Office 365 and remote access
- Document delegation to Active Directory
- Secure the domain administrator account
- Do not install additional software or server roles on DCs
What Are Some Common Threats to Active Directory Security?
Domain Users with Local Admin Privileges
When regular domain users are granted local administrator rights on their workstations, it opens up a broad attack surface. If such an account is compromised, whether through phishing, malware, or credential theft, the attacker can gain administrative control over the machine. From there, tools like Mimikatz can be used to extract cached credentials of other users, including administrators, allowing the attacker to move laterally across the network.
Weak and Reused Passwords
Passwords remain one of the weakest links in AD security. Users often choose simple, easy-to-guess passwords or reuse them across multiple systems. If any of these credentials are leaked in a third-party breach, attackers can use them to gain unauthorized access to Active Directory via credential stuffing or password spraying attacks. Once inside, an attacker can enumerate domain users and attempt to pivot to accounts with higher privileges.
Brute Force Attacks
Brute force attacks involve automated attempts to guess usernames and passwords by systematically trying combinations until the correct one is found. In AD environments with weak or default credentials and no lockout policy, these attacks can be highly effective. Attackers may target exposed services like Remote Desktop Protocol (RDP), VPNs, or web-based logins integrated with AD.
Overuse of Domain Accounts
Domain accounts are often used unnecessarily for routine tasks such as running services, executing scripts, or accessing internal applications. When these accounts have elevated privileges, they become high-value targets for attackers. Their frequent use increases exposure and the likelihood that their credentials will be cached or stored in memory on multiple systems. It’s critical to separate administrative accounts from day-to-day user accounts.
Overprivileged Service Accounts
Service accounts are often created with permissions far beyond what they actually require, either for convenience or due to poor visibility into their real usage. Many of these accounts are configured with domain admin rights, never expire, and use static passwords that remain unchanged for years. These conditions make them ideal targets for attackers looking to escalate privileges and maintain long-term persistence within the domain.
Insider Threats
These type of threat exploits human error or uses malicious intent to gain access. Common examples include:
- Phishing and social engineering: Deceptive tactics like fake emails or phone calls can trick users into revealing their credentials, handing the keys to the attackers.
- Spear-phishing: Personalized attacks targeting specific individuals with tailored messages are even more effective.
- Excessive permissions: Granting users more access than necessary creates opportunities for misuse, intentional or accidental.
Active Directory Security Best Practices
Active Directory policy best practices are crucial for optimal system functioning. They enhance security, prevent data loss, and ensure efficient operations. Following is a comprehensive list of Active Directory security best practices:
1. Find and Remove Unused User and Computer Accounts
Stale accounts present a major security risk. Unused user accounts can be hijacked by attackers and leveraged to access internal resources without drawing attention. Similarly, inactive computer accounts can be exploited in replay or ticket-based attacks if still associated with a domain.
Use tools like PowerShell or Microsoft’s Active Directory Administrative Center to identify accounts that haven’t been used in a defined time window—commonly 30, 60, or 90 days. Disable them first to validate they’re no longer needed, and then remove them entirely. This cleanup process should be done regularly and automated where possible.
2. Use at Least Two Accounts
Administrators should separate their everyday user account from their privileged admin account. Using a single account for both tasks increases exposure—especially if that account gets phished or compromised while performing non-admin functions like browsing or checking email.
Daily non-administrative tasks should be performed using standard user credentials. Administrative tasks should only be conducted using a dedicated account that is protected with stricter controls such as multifactor authentication (MFA), audit logging, and constrained access to management systems.
3. Remove Users From the Local Administrator Group
Allowing regular users to retain local administrator rights on their workstations significantly increases risk. It enables the installation of unauthorized software, manipulation of system settings, and potential elevation of privileges for attackers if the machine is compromised.
Audit all domain-joined machines for local administrators and remove non-essential users. Use Group Policy or tools like LAPS to manage required administrative access in a controlled, time-bound manner. Where needed, deploy privileged access management (PAM) solutions to handle just-in-time elevation.
4. Monitor DNS Logs for Malicious Network Activity
DNS logs can provide early indicators of compromise, such as communication with known command-and-control servers, DNS tunneling, or queries for suspicious domains. Attackers often rely on DNS as a covert channel for data exfiltration or malware staging.
Enable DNS logging on Windows DNS servers and aggregate logs into a central SIEM. Use detection rules to flag abnormal patterns like high volumes of NXDOMAIN responses, base64-encoded domains, or excessive external queries. Cross-reference logs against threat intelligence feeds for known malicious domains.
5. Disable the Local Administrator Account on All Computers
The default local administrator account is a prime target because it exists on every Windows machine and often has the same password across systems. If not disabled or managed, this account can be exploited to gain local or even domain-wide access.
Use Group Policy to rename and disable the built-in Administrator account. If local admin access is required, implement LAPS or gMSAs to manage unique, randomized passwords for each system. Ensure logging and alerting are enabled for any attempts to use this account.
6. Lock Down Service Accounts
Service accounts are often over-privileged and poorly monitored, making them attractive targets for attackers seeking persistent access. Many use static passwords and are granted interactive logon rights, which should be avoided.
Audit all service accounts to verify usage and permissions. Apply least privilege principles—restricting access only to the services they support. Where possible, migrate to gMSAs to eliminate manual password management. Disable interactive logon and restrict logon hours and workstations as additional safeguards.
7. Enable Audit Policy Settings With Group Policy
Auditing is critical for detecting unauthorized access, changes to AD objects, and other security events. Without proper logging, it’s nearly impossible to investigate incidents or ensure compliance.
Use Group Policy to enable advanced audit policies, including directory service access, logon events, privilege use, and object access. Direct logs to a centralized log management solution for correlation and long-term storage. Regularly review audit logs to identify anomalies or policy violations.
8. Monitor DHCP Logs for Connected Devices
Rogue or unauthorized devices can connect to the network and access internal resources if not properly detected. DHCP logs provide insight into every device that requests an IP address.
Enable DHCP logging on all servers and review logs for unknown MAC addresses or unexpected device types. Correlate with inventory systems to spot discrepancies. Suspicious entries should be investigated, and unauthorized devices quarantined or blocked via network access control (NAC).
9. Use a Secure Admin Workstation (SAW)
Admin credentials should only be used from hardened, isolated environments. Performing administrative tasks from regular workstations increases the risk of credential theft via malware, keyloggers, or browser exploits.
Deploy Secure Admin Workstations (SAWs) that are dedicated solely to administrative tasks. These systems should be locked down with strict application whitelisting, no internet access, and enhanced logging. SAWs reduce the attack surface and protect privileged credentials.
10. Use Secure DNS Services to Block Malicious Domains
Public DNS resolvers often lack advanced threat filtering, exposing users to malicious domains used in phishing, malware distribution, or command-and-control communication.
Use secure DNS services—such as Microsoft Defender for Endpoint DNS filtering, Cisco Umbrella, or Quad9—that block known malicious domains. These services integrate threat intelligence and can prevent access to harmful content before a connection is even established. Configure endpoints and domain controllers to forward DNS queries through these filtered resolvers.
11. Use Descriptive Security Group Names
Clear and descriptive group names make it easier to understand access rights, reduce misconfigurations, and improve auditing. Vague names like “Group1” or “Admin_Team” provide little insight into the group’s purpose or the resources it controls.
Adopt a consistent naming convention that reflects the function, scope, and sensitivity of the group. For example, “GRP_FS_Read_Accounting” indicates file share read access for the accounting department. Descriptive names help during audits, reviews, and delegation decisions, and reduce the risk of users being added to the wrong groups.
12. Use Latest ADFS and Azure Security Features
Active Directory Federation Services (ADFS) and Azure Active Directory (Azure AD) offer powerful capabilities, but outdated deployments often lack critical security enhancements. Newer versions include better support for modern authentication, conditional access, and improved monitoring.
Ensure ADFS is regularly updated to support the latest protocols (e.g., SAML 2.0, OAuth 2.0, OpenID Connect). In Azure AD, enable features like conditional access policies, identity protection, risk-based MFA, and sign-in risk detection. These tools help reduce exposure and provide fine-grained control over cloud and hybrid authentication scenarios.
13. Use Passphrases
Traditional password policies focused on complexity (uppercase, numbers, symbols) can lead to weak or reused passwords. Passphrases—longer sequences of words or phrases—are more secure and easier to remember.
Encourage users to use passphrases of 14 characters or more, ideally combining unrelated words (e.g., “coffee-planet-window-4”). Passphrases reduce the success rate of brute-force and dictionary attacks. Combine passphrases with MFA for stronger protection without compromising usability.
14. Have a Recovery Plan
If Active Directory is compromised or misconfigured, recovery can be complex and time-sensitive. Without a plan, outages can be prolonged, increasing the risk of data loss or business disruption.
Create a detailed AD recovery plan that includes system state backups, restoration procedures, privileged access recovery steps, and offline copies of documentation. Test the plan regularly in an isolated environment. Include strategies for recovering from ransomware, accidental deletions, and domain controller failures.
15. Limit the Use of Domain Admins and Other Privileged Groups
Domain Admins, Enterprise Admins, and Schema Admins have unrestricted access across the domain. Using these accounts for day-to-day tasks increases the risk of compromise.
Restrict membership in high-privilege groups to the bare minimum. Enforce the use of tiered administration models and just-in-time access via tools like Microsoft Privileged Access Management (PAM) or third-party solutions. Monitor and alert on any changes to these groups or use of accounts within them.
16. Use LAPS
The Local Administrator Password Solution (LAPS) helps mitigate the risk of lateral movement by managing unique, rotating passwords for local admin accounts on domain-joined systems.
Deploy LAPS to store each computer’s local admin password securely in AD and restrict who can view or reset them. LAPS eliminates the use of shared local admin credentials and enforces better control over endpoint administration.
17. Use Two-Factor for Office 365 and Remote Access
Office 365 and remote access solutions are common entry points for attackers, particularly through phishing or stolen credentials. Relying on passwords alone is insufficient.
Enable two-factor authentication (2FA) or MFA for all external access, especially for administrative users and users with access to sensitive data. Use built-in options like Microsoft Authenticator or integrate with third-party providers. Conditional access policies in Azure AD can also enforce 2FA based on risk levels, location, or device compliance.
18. Document Delegation to Active Directory
Delegation in AD allows certain users or teams to perform administrative tasks without giving them full control. Poorly documented or unmanaged delegation can lead to excessive access and security blind spots.
Use the Delegation of Control Wizard or custom permissions to grant only necessary rights. Maintain up-to-date documentation of all delegations, including purpose, scope, and owner. Regularly audit delegated permissions to ensure they remain justified and within scope.
19. Secure the Domain Administrator Account
The domain administrator account is the most powerful in AD. If compromised, it can lead to total domain takeover.
Rename the default Administrator account and disable it where possible. Use a strong, unique password stored securely (e.g., in a password vault). Limit its use to emergency scenarios, and restrict logon to secure systems only. Monitor its use with alerts for any authentication attempts or group membership changes.
20. Do Not Install Additional Software or Server Roles on DCs
Domain controllers (DCs) are critical infrastructure components and should be dedicated to directory services. Installing other roles or software increases attack surface and can introduce conflicts or vulnerabilities.
Avoid running file shares, web services, backup agents, or monitoring tools directly on DCs. These functions should be hosted on separate servers. Keep the DC role isolated to reduce risk, simplify troubleshooting, and maintain performance and stability.
Active Directory Security with XM Cyber
XM Cyber continuously assesses core Active Directory deployments to identify and prioritize issues, while mapping to industry best practices and regulatory standards. Validated attack paths show how attackers can combine Active Directory exposures with other issues such as vulnerabilities or cloud misconfigurations to move laterally in your environment and compromise business critical assets.