FIX WHAT MATTERS
Continuous Exposure Management. Without the Noise.
Continuously discover, prioritize, and fix every validated
exposure that leads to your critical assets.
KNOW WHERE YOU’RE EXPOSED
The Only Exposure Management Platform that Anticipates & Eliminates Every Viable Attack
Continuous monitoring at scale
Natively built to continuously monitor your hybrid environment with agent-based and agentless discovery of every asset and every exposure, including security controls, shadow AI, AI services in the cloud and on-prem, and AI policy violations.
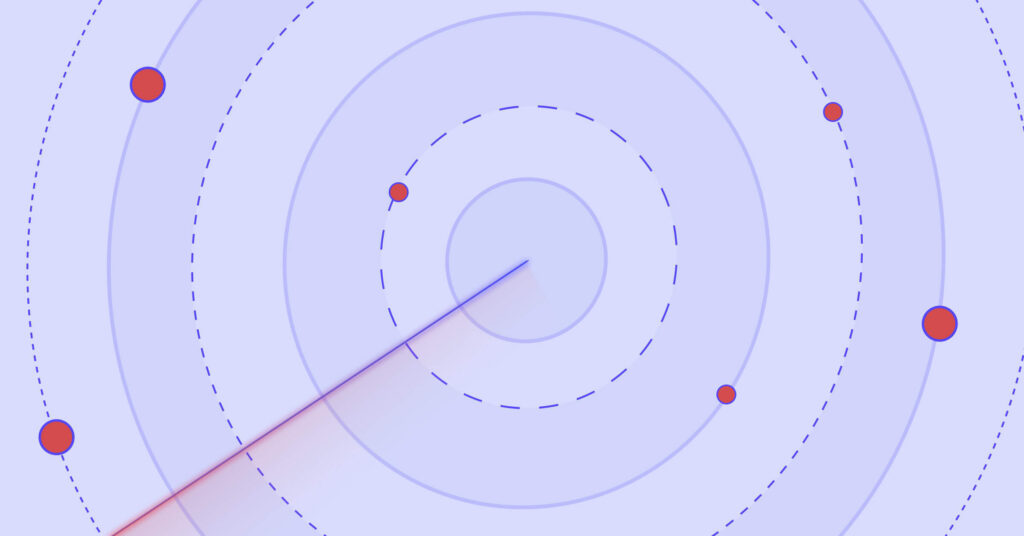
End-to-end discovery across the full attack surface
Discover how attackers can move across your network by chaining , misconfigurations, identity exposures, over-privileges, and AI exposures into attack paths spanning on-premises and multi-cloud environments, from the external attack surface all the way to critical assets.
True validation of exposures to filter out noise
Build a digital twin of your overall environment to validate the exploitability and reachability of every exposure and every attack path by checking all conditions across assets, networks, and compensating security controls.
Business-driven prioritization
Prioritize the exposures that compromise the highest number of critical assets and sit at intersections of multiple attack paths (Choke Points) – so a single fix eliminates multiple paths.
Share impact insights for driving effective remediation
Share unique exposure intelligence context across teams and security solutions to align on a common sense of urgency. Drive effective, actionable remediation with clear guidance, alternatives, and automated ticketing and verify resolution with remediation confirmation.
Meaningful risk and compliance reporting
Report on significant reduction of risk to critical assets to prove reliable resilience to leadership. Achieve continuous audit readiness by monitoring security controls for policy violations and configuration drift in accordance with regulatory frameworks
Continuous Exposure Management
Natively built for high scalability and integrated into your security stack
XM Attack Graph Analysis™
Turn Millions of Exposures into a Shortlist of the Ones that Must Be Fixed First
XM Attack Graph Analysis™ maps all viable exposures into attack paths – from your external attack surface, across on-prem and cloud, to your business-critical assets. The platform takes a digital twin approach to prioritize only the exposures that are validated against real exploitability and reachability conditions, taking into account compensating security controls in your environment.
Challenging the Status Quo
XM Cyber Named a Challenger in the First-Ever 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms

The product is easy to deploy, easy to handle and configure, and gives great and important insights from the attacker׳s point of view.
IT Security and Risk Management – Manufacturing

This tool allows you to define quick-win remediation but, more importantly, focuses on compromising paths to its most critical assets.
IT Security and Risk Management – Banking

Best CTEM feature solution currently on the market. The usability and product features are innovative to me and work well.
IT Security & Risk management – IT Services