XM Cyber and FC Bayern Munich
Protecting Fans Through Digital Sovereignty
XM Cyber and STIHL
Securing a Global Legacy Through Digital Sovereignty
XM Cyber and VfB Stuttgart
Building a Secure Digital Future Together
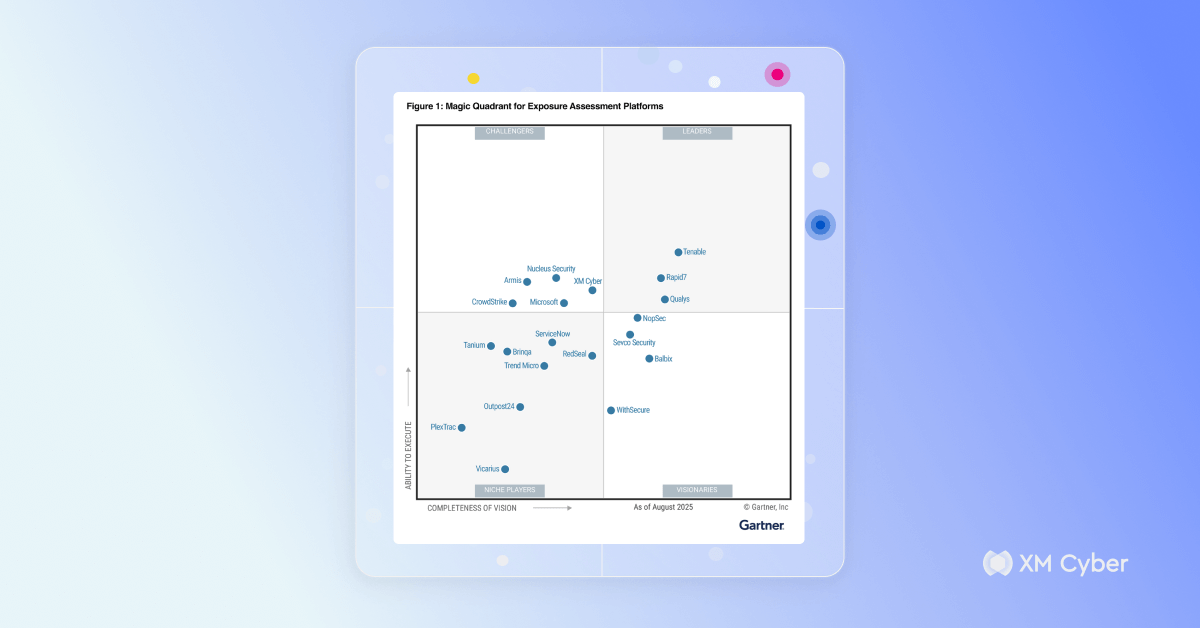
XM Cyber Named a Challenger in 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms
Challenge Accepted!
XM Cyber Named a Challenger in the 2025 Gartner® Magic Quadrant™ for Exposure Assessment Platforms
XM Cyber Helps Clal Insurance Gain Visibility and Save Time in Security Operations
How to Build a Continuous Exposure Management Plan from Scratch
XM Cyber Helps an Italian Public Sector Organization Quantify Risk and Strengthen Security Posture
Case Study: Jerome Monot, IT Security Manager for Rothschild & Co.
From Alerts to Action: Streamlining Remediation Operations with Continuous Exposure Management
What are Exposure Assessment Platforms?
Flipping the Script: Seeing Risk the Way Attackers Do
Request a demo