From Alerts to Action: Streamlining Remediation Operations with Continuous Exposure Management
What are Exposure Assessment Platforms?
Flipping the Script: Seeing Risk the Way Attackers Do
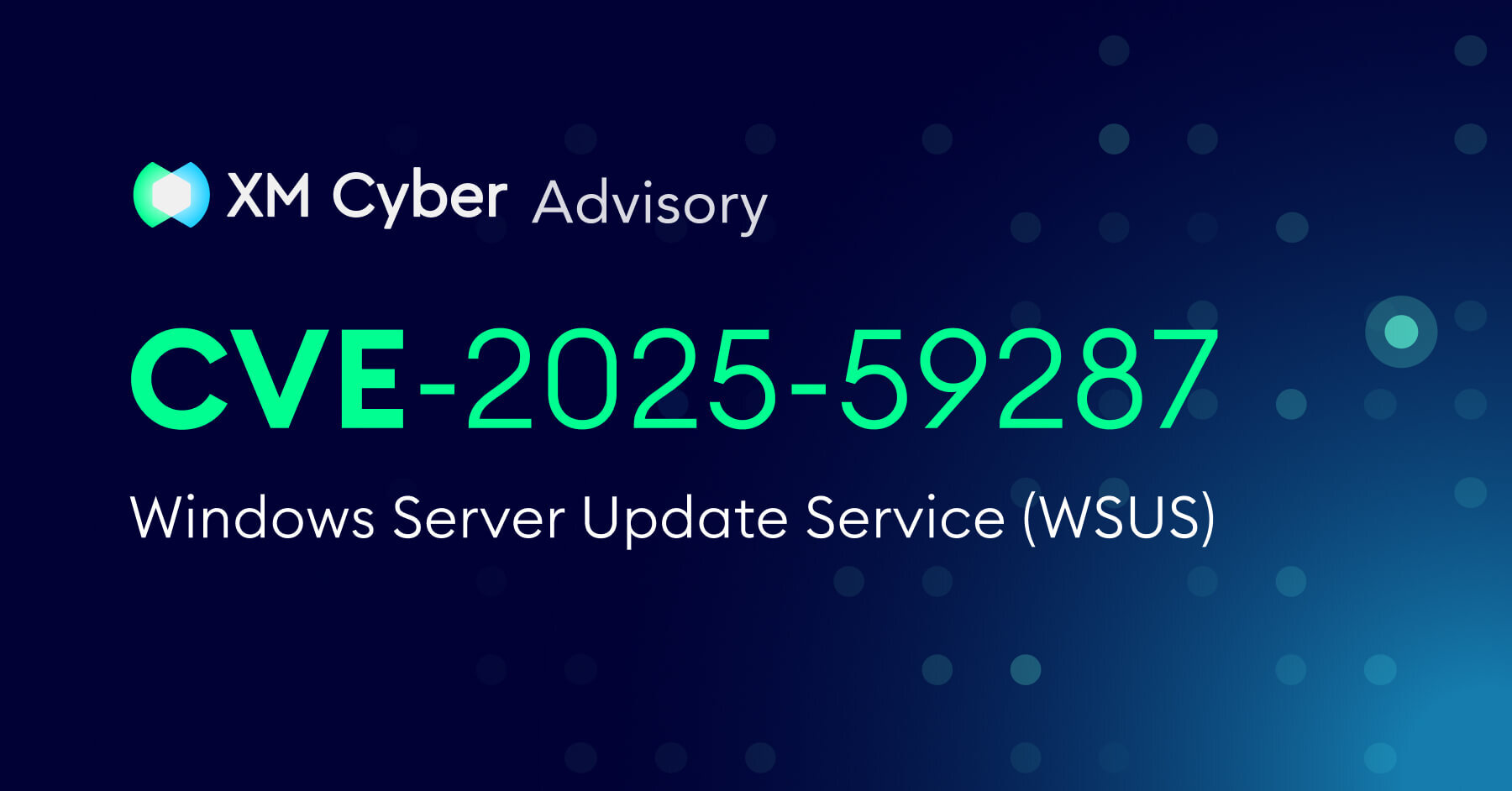
Windows Server Update Service (WSUS) Critical Vulnerability: CVE-2025-59287 Under Active Exploitation
XM Cyber Helps Jerusalem Municipality Strengthen Security and Gain Visibility
XM Cyber Helps Lidl Spain Focus on What Matters Most
XM Cyber Helps Golf Club St. Leon-Rot Gain Visibility and Strengthen IT Security
Cracking the Boardroom Code: A New Path for CISOs
CRITICAL ALERT: Oracle E-Business Suite Zero-Day Vulnerability, CVE-2025-61882, Under Active Exploitation!
Can CTEM Address the Hidden Gaps in Your PAM Program?
Stop Wasting Time on Endless Exposures. Fix What Matters.
Zero Trust & Exposure Management: Your Path to Proactive Security
See XM Cyber In Action