While the spring/summer 2019 fashion colors on runways in New York, London, Milan, and Paris may be pink, lilac or lavender, when it comes to preventing both the scariest or even the most surprisingly unsophisticated cyber attacks, the shade gets a bit darker. In cybersecurity, purple is the new black!
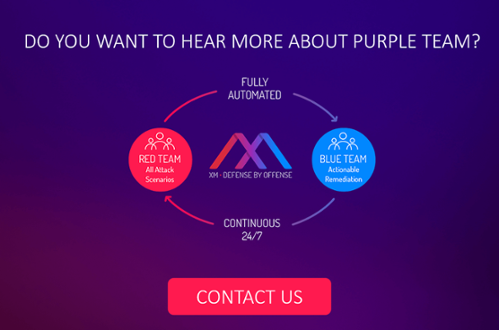
You have probably heard the terms red team and blue team being tossed around in the context of cybersecurity. Indeed they have been around for a long time among numerous organizations and government agencies. But are you familiar with why purple teams are a key accessory to secure your company and mainly why they’re considered a hot trend mainly when automated? If not, don’t worry, they won’t go out of fashion so soon.
Cybercrime is a fast-growing industry and with no signs of slowing down. In 2018, the cybercrime economy was estimated to be worth $1.5 trillion, reported The Fintech Times. Activities around it – from how it is perpetrated to its methods of spread – are becoming more and more creative. Red, blue and purple teaming are all components of the evaluation of a network’s/system’s overall security posture.
Red Team & Blue Team: Be Dressed to Kill Attackers
Let’s check every season’s basics:
- Red Team – It’s a dedicated group that challenges an organization to improve its effectiveness by assuming an adversarial role or point of view. It assesses security methodologies as if through the eyes of the attacker. Such exercise is a hallmark of the information security lifecycle due to its ability to identify systemic risk that most usually had not been taken into account.
- Blue team – It’s a group of individuals who perform an analysis of information systems to ensure security, identify security flaws, verify the effectiveness of each security measure, and to make certain all security measures will continue to be effective after implementation. A blue team is a company’s own cybersecurity or IT personnel, who are trained to work on defending and improving their organization’s defenses around the clock.
In a nutshell: the former (as the good guys they are) attacks, the latter defends. Companies in any industry can benefit from a highly realistic red team-blue team exercise. But, still, is that enough to fight cybercrime today? To what extent can organizations’ red and blue teams dedicate time and effort to achieve this goal in addition to their everyday attributions with efficiency and continuity?
Why a Purple Team Is On-Trend
Many red and blue teams have worked very much in silos. In some cases, some can get out of sync with each other. A purple team should not be a group that fills or replaces both red and blue roles, but rather a function that enhances their existing capabilities and allows them to exchange ideas, observations and insights more productively.
You don’t need to be a cyber fashionista to agree that all three “colors” share the ultimate purpose of improving the organization’s defenses. Red does this through “ethical attack”, blue through defense, and purple by ensuring that the previous two are cooperating.
Simulation & Remediation – Automated Purple Team Is a Must-Have This Season
With an automated purple team running continuously, organizations will finally know as soon as an issue has been resolved and be able to follow prioritized remediation guidelines. The move to automation empowers organizations with the ability to gain a worm’s eye view into new back doors and blind spots as soon as they appear and move to remediate them immediately without delay.
XM Cyber provides the first fully automated breach and attack simulation (BAS) platform to continuously expose attack vectors, from breach point to any organizational critical asset. This continuous loop of automated red teaming is completed by ongoing and prioritized actionable remediation. In effect, its platform operates as an automated purple team, combining red and blue teams’ processes to ensure that organizations are always one step ahead of the attack.
XM Cyber’s HaXM solution empowers organizations to observe the gaps in their cybersecurity posture and continuously challenging their network. They gain clear visibility of the cyber risks, and an efficient, data-driven actionable remediation plan aimed at the most burning issues to fix.
Green Light from Trendy Experts
“XM Cyber has developed a technology that identifies and exposes all attack vectors. These include lateral movement from breach points to an organization’s critical assets, otherwise left undetected by security controls. It delivers automated and continual simulation of red team activity and completes the cycle by providing recommendations for how best to remediate the security holes it has identified in a corporate network,” concluded a 2018 Ovum report.
For Pierluigi Paganini, Cyber Defense Magazine’s editor-in-chief, XM Cyber is a game changer.
“With cybercrime continuing to gain momentum, surpassing global drug crime last year, we see XM Cyber as a multi-award-winning innovator, offering a new approach to defeat these criminals,” he declared during the RSA Conference 2019.
While we blush – not of shame, but rather of excitement – we hope you’re convinced that the color red and blue make when mixed is here to say when it’s about fighting cybercrime. Don’t see red every time there is a new scary cyberattack out there. Don’t be blue anymore either. Purple is the new black, baby!
Related Topics