|
Getting your Trinity Audio player ready...
|
Cyber Risk Quantification (CRQ) is a vital process in cybersecurity that calculates the potential impact of risk in terms that make sense for your business.
CRQ helps organizations align their security strategy with their broader business goals. The shift of CRQ has precipitated a wider shift in the cybersecurity conversation – from technical details and data centers to practical issues in the boardroom. This is helping executives understand potential threats, prioritize actions and make better decisions about cybersecurity and how to best mitigate cyber risks.
Cyber Risk Quantification has become a crucial part of strategic planning. It guides executives to invest in cybersecurity measures that not only protect the organization from potential threats but also align seamlessly with its overall business objectives.
Why is Cyber Risk Quantification Important?
Cyber Risk Quantification is increasingly important for several reasons:
- The increasing complexity of cyberattacks – The surge in the sophistication and aggressive nature of cyberattacks has made CRQ a must-have. As cyber threats become more complex, there is a growing need for smarter assessment, measurement, and response strategies.
- Expanding attack surfaces – The adoption of AI, IoT, robotic process automation, and the cloud by businesses has dramatically grown their attack surfaces, providing cybercriminals with numerous entry points. To stay ahead, a precise understanding of risk impact and likelihood is essential.
- Limited cybersecurity budgets and resources – Organizations are struggling with multiple IT and cyber risks, making prioritization an urgent imperative. CISOs need to allocate limited budgets strategically – determining which risks and security controls offer the most efficient outcomes. Cyber Risk Quantification guides investment decisions by quantifying potential financial losses and assessing the cost-effectiveness of specific controls.
- Qualitative measurements fall short – Historically, cyber risks have been communicated qualitatively, using terms like “probably likely” or “somewhat likely.” However, these qualitative descriptions often raise more questions than answers. To address uncertainties and make informed decisions, there is a growing need for quantitative data that provides a clear-cut determination of risk probabilities and the efficacy of various mitigation options.
What are the Benefits of Cyber Risk Quantification?
Quantifying your cyber risk with Cyber Risk Quantification methods yields numerous advantages for your organization.
Firstly, CRQ facilitates more efficient resource and budget allocation – ensuring that your investments in cybersecurity align with the actual risks your organization faces. CRQ also enables the prioritization of risks, allowing your organization to focus efforts on addressing the most significant threats. What’s more, Cyber Risk Quantification fosters improved communication and trust between security and executive leaders – it bridges the gap between cybersecurity experts and executive decision-makers by translating technical details into financial impacts.
Furthermore, CRQ empowers your organization to track the effectiveness of cybersecurity programs over time. It is valuable for assessing the impact of security investments and making informed adjustments as needed. Through the lens of Cyber Risk Quantification, your organization gains the capability to answer critical questions – like understanding the expected financial loss from cyberattacks, evaluating the adequacy of security investments, identifying necessary adjustments to reduce cyber risk, and pinpointing which risks carry the most substantial financial impact.
The Challenges of Quantifying Cyber Risk
Despite the crucial role that Cyber Risk Quantification plays for organizations, implementing a CRQ program can pose significant challenges, notably:
- Insufficient visibility – While organizations may possess numerous tools that generate data, it is often challenging to sift through the abundance of information to identify actual risk indicators. Gaps in your asset inventory can further complicate matters, making it harder for security leaders to accurately assess cyber risks and vulnerabilities. The end result of insufficient visibility is a limited understanding of the effectiveness of existing security tools.
- Complex risk calculation – Unifying data into a standardized risk model is challenging due to differing formats and semantics across different tools. Discrepancies in how attributes are represented for assets and users can lead to conflicting information. Moreover, diverse stakeholders often use different terminology, making it difficult to reconcile diverse perspectives into a universally understood risk metric.
- Incomplete remediation – New vulnerabilities and threats emerge hourly – making it a challenge to identify, prioritize, and address risks. The primary goal of cybersecurity is to keep ahead of threat actors, yet a lack of real-time information holds security teams in streamlining protective processes. Automatic and continuous visibility into the attack surface and emerging security issues is essential for organizations to remediate risks promptly and effectively. Lacking this, organizations have difficulty fully remediating known risks.
How Do You Quantify Cyber Risk?
Quantifying cyber risks attributes a monetary value to the impact of potential cyber threats. This process is inherently reliant on data and tailored to specific use cases. In the context of cybersecurity metrics like cyber resilience and risk quantification models, the focus often centers around data breach susceptibility.
The foundational formula for quantifying risk is expressed as:
{Data Breach Risk} = {Breach Likelihood} X {Breach Impact}
Here, Data Breach Risk is represented in dollars, Breach Likelihood as a percentage, and Breach Impact as a monetary value.
Given the increasing complexity of attack surfaces, CRQ calculations must account for the distinct risk exposures of each IT asset. While some assets may be more resilient to cyber threats, even those which seem less critical can be attack vectors – meaning they need to be included in data breach risk assessments. Because of this, it’s crucial to map the entire attack surface before embarking on a CRQ program. Automation technology is invaluable to help address this need, especially given the vast and continually expanding modern attack surfaces.
Security ratings are also important precursor metrics for CRQ. This practical measurement offers a real-time snapshot of security postures and the impact of emerging risks. Using security ratings technology helps show how a given action might affect the potential impact of a threat.
Five Best Practices for Cyber Risk Quantification
To get maximum value from your Cyber Risk Quantification program, adhere to the following best practices:
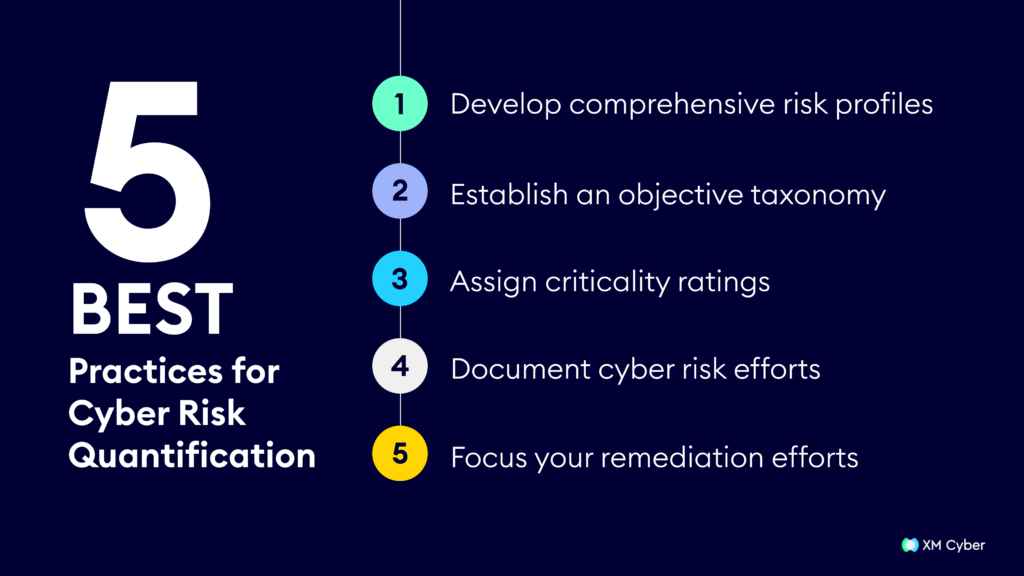
- Develop comprehensive risk profiles – Summarize threats affecting both internal and external landscapes. Facilitate the process by encouraging vendors to share their profiles.
- Establish an objective taxonomy – Ensure effective communication within the organization by adopting an objective list of cybersecurity definitions. This minimizes confusion arising from interchangeable use of cyber terms.
- Assign criticality ratings – Streamline cyber risk quantification by assigning criticality ratings to all assets, internal and external. Utilize risk matrices to represent severity distributions, especially for third-party vendors that may be crucial attack vectors.
- Document cyber risk efforts – Maintain accessible documents summarizing cyber risk calculations to support spontaneous decision-making and enhance the scalability of cybersecurity programs.
- Focus your remediation efforts – Avoid overwhelming security teams by concentrating on cyber threats with the highest damage potential. Prioritize risks based on a comprehensive strategy that incorporates various techniques like cyber risk quantification, vendor tiering, and security ratings.





