Stop the SOC Burnout: Fixing the Alert Fatigue Crisis
Alert fatigue is one of the most persistent and costly problems in security operations – and it’s getting worse. According…
Blog
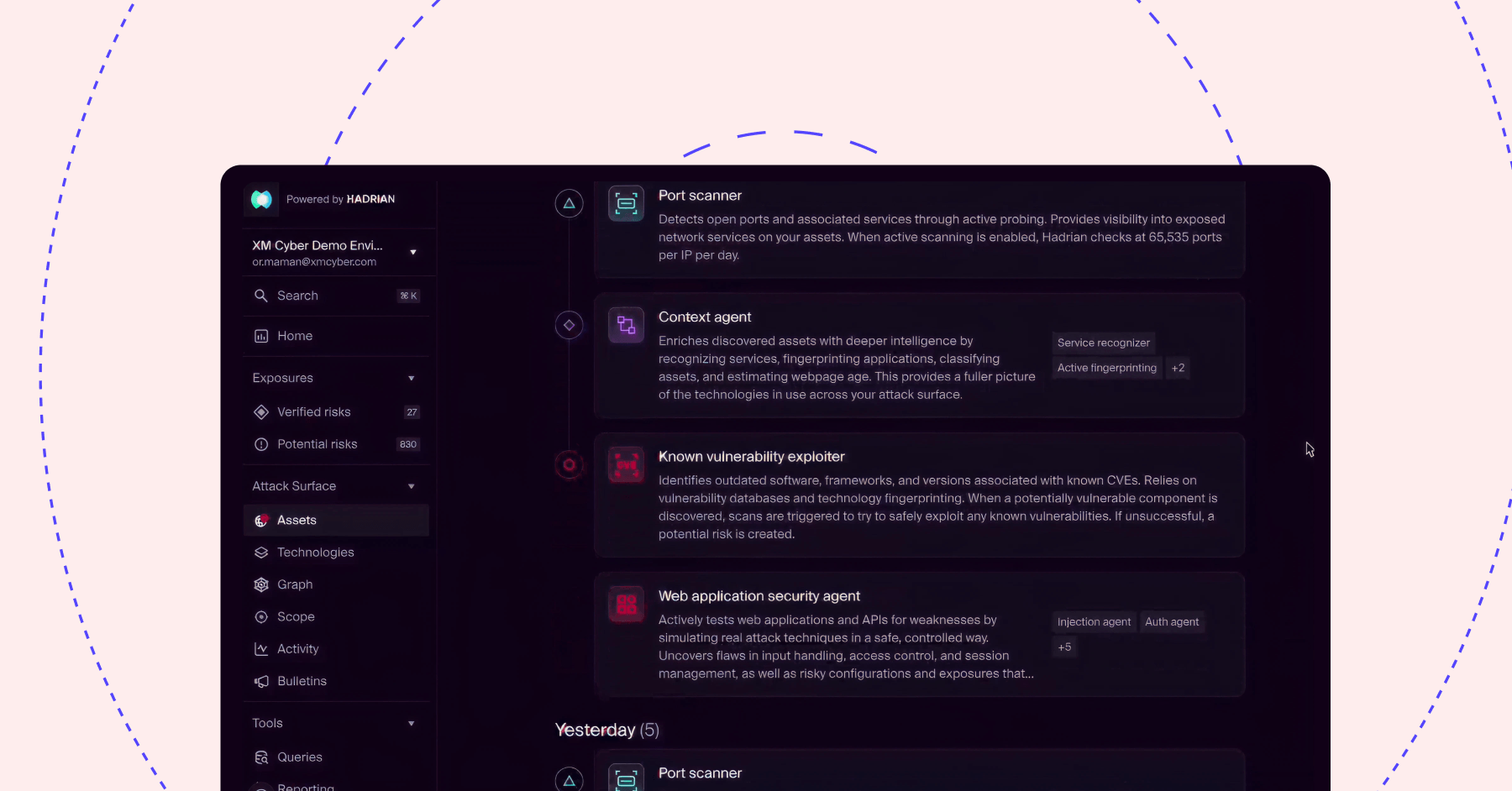
External Attack Surface Management (EASM)
XM Cyber links the external attack surface directly to the blast radius of external exposures on critical business assets. Watch…
Videos
Cloud Exposure Management
Prevent cloud breaches by proactively eliminating exposures and validated attack paths that put your business-critical workloads at risk.
Solution Briefs
Building and Scaling Secure Agentic AI Applications in AWS Bedrock
The transition from passive Generative AI to Agentic AI has fundamentally rewritten the cloud security playbook. While early defenses focused…
eBooks & Whitepapers
XM Cyber Continuous Exposure Management
Check out what makes XM Cyber’s Continuous Exposure Management platform unique so you can finally get exposure prioritization right and…
Videos
Security Controls Monitoring
Continuously assess tool configuration, optimize defenses and streamline compliance.
Solution Briefs
Identity Exposure Management
Continuously monitor for identity and access-related exposures across your hybrid environments. Remediate validated attack paths before attackers can exploit them.
Solution Briefs
Vulnerability Scanners Cannot Power Your CTEM Program
Most CISOs I’ve worked with understand intuitively that vulnerability scanners – like any tool in the security stack – have…
Blog
Seeing Through the Eyes of An Attacker: Validating Exposures from External Breach Points to Internal Critical Assets
To catch a criminal, you need to think like a criminal. This is not a new concept, and it’s one…
Blog
Beyond the Patch – Why Frost & Sullivan Named Us Leader for the 2nd Time in a Row in ASV
It’s well known that security teams are often drowning in alerts. And considering that 74% of identified exposures are actually…
Blog
See XM Cyber In Action